Incident Overview
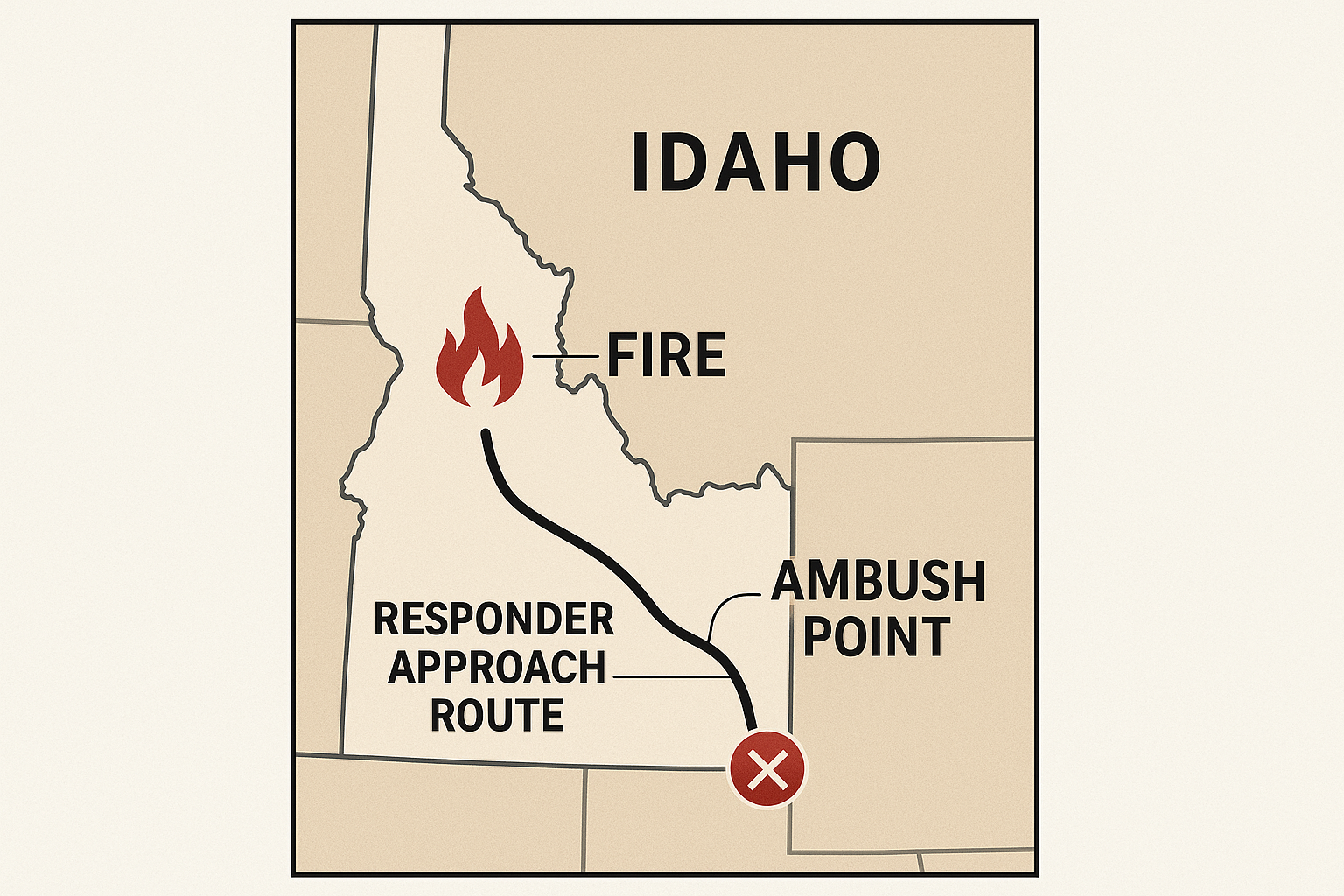
On June 29, 2025, a lone attacker ignited a brush fire on Canfield Mountain, Idaho, to draw firefighters into a secluded area before opening fire, killing two and critically wounding a third. The suspect, 20-year-old Wess Roley, was later found deceased after a multi-agency manhunt.
The Emerging Threat Pattern
Roley’s tactic—using deception to exploit predictable response timelines—mirrors a broader trend in the asymmetric targeting of emergency personnel, especially in rural areas where responders operate with limited law enforcement support.
“Traditional wildfire protocols are now a vulnerability when adversaries weaponize terrain familiarity and response predictability.”
Protective-Intelligence Perspective
| Threat Vector | Vulnerability | Countermeasure |
| Brush-fire lure | Isolation of wildland crews | Pre-dispatch OSINT sweep & drone overwatch |
| Terrain advantage | Limited situational awareness | Forward security staging & remote sensors |
| Lone-actor ideology | Minimal pre-incident indicators | Behavioral-threat monitoring & local intel briefs |
Actionable Measures for Agencies
- Pre-Deployment Threat Scanning – Integrate OSINT/SIGINT tools to flag suspicious fire calls in remote zones.
- Protected Staging Protocols – Establish security overwatch before crews advance on uncontrolled fires.
- Embedded Intel Liaisons – Pair field crews with trained threat-assessment personnel for high-risk calls.
- Remote-Area Surveillance – Utilize drones or thermal imaging linked to GSOC for real-time visibility.
- Secure Comms & Duress Alerts – Issue encrypted devices with panic-beacon capability.
- Behavioral-Threat Training – Train crews to recognize pre-attack indicators during routine responses.
How The North Group Supports High-Risk Professions
You face escalating, intentional threats. Our Protective-Intelligence Programs combine 24/7 GSOC monitoring, embedded security liaisons, and rapid-response teams to keep your crews safe and mission-focused.

Conclusion
The Canfield Mountain ambush is a stark reminder: in today’s threat landscape, courage alone is not enough. Predictive intelligence, disciplined protocols, and integrated security support are now mission-critical for every agency that answers the call.